People are the weakest link in all computer systems. We hear about the best cryptography money can buy: integrity checking, sender/receiver identity authentication, digital signatures, and then someone leaves a list of passwords on a post-it note stuck above a computer and in an instant renders all the algorithms pointless. Or the same someone automatically gives out his password over the telephone or by email when ‘technical support’ asks so that they can reset it – another victim of phishing.
Cryptography, according to Wikipedia, is the study and practice of hiding information. Many of us assume that it is all about computers and mathematics, which it is of course, but then since information is power, keeping a secret or trying to intercept someone else’s news is the most human of all activities and as old as time itself.
Intercepting messages began in Edward II’s reign and Elizabeth I had a whole spy network. This eventually led to a secret man in the post office and then a secret department which led to a secret service as we know it today. It is not for no reason that James Bond is portrayed as a playboy. Many spies were motivated solely by cash to support such a glamorous lifestyle and would therefore, report to the highest bidder.
The human is essential to cryptography
In the same way the science of cryptography began with the human element and only much later on was it taken over by mathematicians and computer geeks. During the two World Wars, classicists were employed to decode the enemy’s messages. They seemed the best people to do so because that is how they spent their time ordinarily.
Classicists wanted to know what the Rosetta Stone said or whether Francis Bacon had written some of William Shakespeare’s plays, and they did this by studying and deciphering seemingly cryptic texts. It was only during WWII that mathematicians got in on the act. One of the most famous deciphering stations, Bletchley Park needed as many cryptographers as possible, so ringing round the banks to keep the place staffed brought in the mathematicians.
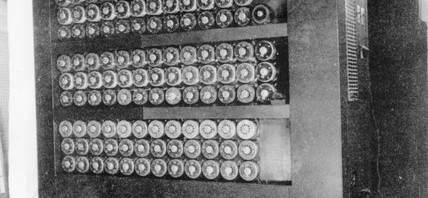
Cipher machines such as the German Enigma machine originated in commercial banking during peacetime. Keeping information secret allowed banks to maintain their competitive edge and banks invested in the technology. During wartime when the need for national security was high, these machines were adapted by all sides.
Only human
Whether a playboy spy or a classicist, we are all motivated by something and sometimes this can led us to making errors, even in wartime when people are supposed to be at their most vigilant. In 1916 a drunken German commander in the Middle East sent out exactly the same Christmas message to his six outposts using six different ciphers (or codes). This allowed the British to crack the codes.
During WWII, code breakers looked for human weaknesses to help them crack their codes. A WWII Polish code breaker Marian Rejewski, who worked on decoding the unbreakable German Enigma messages, assumed that operators would choose simple setting like ABC rather than complicated ones. Once the code breakers learnt and used these assumptions it was much simpler for them to break codes.
British code breaker John Herivel was also similarly inspired. He thought about how operators would use a machine in the middle of the war. He thought about the order in which he would set up a machine and whether he do so properly and change the cipher settings. Or would he just shut the machine down and forget about it and then reuse the same settings the next day? This became known as the Herivel tip which played a big part in breaking the Enigma machine.
Lazy operators often used the same messages or the same code settings, such as the operator who was having a cigarette and kept pressing the letter L instead of choosing different letters. This allowed the interceptors to decipher that day’s settings. Operators would use similar greetings as the start of messages which allowed code breakers to see different ciphers containing the same messages. Others would use the same letters before transmitting every message – their girlfriends’ initials or lucky words. Interceptors would not only have a head start in cracking codes but they could also track these operators and gain information about enemy movements.
We are all unique
As we have seen above, it wasn’t just human error which helped code breakers; it was the sense of the individual himself which helped. Interceptors could identify commonalities in messages as they got to know operators. They learnt the way operators spoke in messages and recognised the idiosyncrasies of the operators’ machines by the location of wheel turnover points. Interceptors could also identify and stereotype reports of input and output numbers such as those representing the movement in concentration camps and eventually crack what they meant.
Radio finger-printing identified certain message transmitters. These messengers used Morse Code but still had their own unique styles of transmitting which they never thought to disguise. Interceptors could build up pictures of these individuals and over time identify reports and movements of certain personalities.
Knowing your user
Nowadays interaction designers and usability consultants spend a lot of time studying the user in computer systems using ethnography in the field like the Herivel tip, or building up a task analysis (or sequence of events) that the user performs like Rejewski did. After WWII two new fields of research opened up which recognised our need to better understand humans. Artificial Intelligence and Cognitive Science came to the fore in the fifties so that we could better understand how the human perceives, reasons and acts. After 50 years of research, we realise we still have a lot to learn. We still do not know how the brain works but we do know more about human motivations.
Security systems developers don’t spend as much time on the human as they should. It doesn’t matter how great your algorithms are, if you haven’t factored in human behaviour, your security will be compromised. The unbreakable Enigma was cracked because of human weaknesses.